Exchange Vulnerability Patch
A critical vulnerability in the Microsoft Exchange Server was patched by Microsoft Corp. this month. If an attacker were able to exploit the flaw, they could use it to compromise a business email server and steal valuable data. This vulnerability is not limited to small companies, though; it affects large enterprises and is present on all supported versions of the software. This article will discuss the vulnerability and its remediation. Read on to learn more.
During a recent attack, an attacker was able to compromise an Exchange Server and gain access to its Active Directory. Once they gained access to the Active Directory, they could use this information to steal credentials and impersonate authentic users. This would lead to fraud and phishing attacks. This flaw is known as the ProxyLogon vulnerability and is used to conduct pre-authentication SSRF attacks. It is also vulnerable to Padding Oracle attacks, which require an authenticated user cookie.
There are two ways to implement this patch. One way is to use a script called Exchange Server Health Checker to inventory your Exchange servers that are behind on updates. Another way is to use the Microsoft Exchange Emergency Mitigation (EM) feature to automatically apply interim mitigations to high-risk security bugs. This feature allows administrators extra time to install the security update. This Microsoft Exchange vulnerability is not limited to Exchange servers; it affects the servers that are internally facing.
Microsoft Exchange Vulnerability Patch
The vulnerabilities that affected Microsoft Exchange Servers are known to be exploited in the wild. The CISA partnership has noted that the vulnerabilities are actively exploited in on-premises deployments. Exchange Online customers are protected from the attacks, but attackers who successfully exploit the flaw could gain persistent access to the enterprise network. Sophos experts are recommending that enterprises install the latest patch for their exchange servers. This will prevent attacks from exploiting these vulnerabilities.
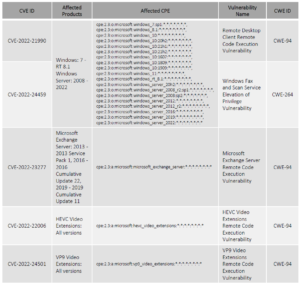
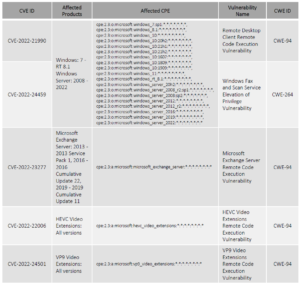
The latest update to the Microsoft Exchange software has outlined the latest exploitable vulnerabilities. CVE-2021-42321 and CVE-2021-42292 are two examples of such vulnerabilities. The CVE-2021-42321 vulnerability is a post-authentication remote code execution flaw. This vulnerability could even lead to an elevation of privilege, which could allow attackers to control a server. Fortunately, a patch for this vulnerability has been released by Microsoft.
As part of Patch Tuesday, Microsoft released security updates for 71 CVE-numbered vulnerabilities. Three of them were previously unknown critical flaws, but had not been exploited. The latest CVE update addressed the Remote Desktop Client vulnerability, which could allow attackers to execute arbitrary code. The patch also addresses the Microsoft Exchange Server vulnerability. This vulnerability is also critical. As of March 20, it is recommended that organizations update their servers to the latest version to prevent the risk of exploitation.